Content Delivery Networks (CDNs) play a pivotal role in optimizing website speed by efficiently delivering content to users worldwide. Understanding and implementing best practices for CDN utilization are essential for enhancing website performance and user experience.
Understanding CDN Functionality:
Content Delivery Networks are distributed networks of servers strategically positioned across various geographical locations. CDNs cache websites content, such as images, CSS files, JavaScript, and videos, across these servers. When a user accesses a website, the CDN serves the cached content from the server closest to the user’s location, minimizing latency and accelerating page load times.
Best Practices for Optimizing Website Speed with CDN:
Selecting the Right CDN Provider: Choosing the ideal Content Delivery Network (CDN) provider is foundational to website optimization. Evaluate providers based on several critical parameters to ensure compatibility with your website’s unique needs and traffic patterns. Consider aspects such as:
- Server Coverage: Assess the geographical presence of servers to ensure extensive coverage across target regions. A global network reduces latency and enhances content delivery speed.
- Network Latency: Evaluate network latency metrics offered by the CDN provider. Lower latency ensures faster content retrieval and quicker page loading times.
- Uptime and Reliability: Examine the provider’s uptime guarantees and reliability track record. A reliable CDN ensures consistent access to your website content without interruptions.
- Security Features: Scrutinize the security measures offered by the CDN, including SSL support, DDoS protection, and web application firewalls. Ensure they align with your security needs.
- Scalability: Verify the CDN’s ability to scale alongside your website’s growth. A scalable CDN accommodates increased traffic demands efficiently.
- Customer Support: Assess the quality and responsiveness of the CDN provider’s customer support. Timely and effective support is crucial during troubleshooting and optimizations.
Caching Strategies: Implementing effective caching strategies is pivotal for optimizing content delivery. Utilize CDN caching for both static and dynamic content. Configure cache expiration headers appropriately for different content types to strike a balance between content freshness and load times. Employ intelligent cache control mechanisms to ensure frequently accessed content is readily available while being regularly updated.
Optimizing Content for Delivery: Content optimization significantly impacts delivery speed. Compress images and files to reduce their size without compromising quality. Utilize modern image formats and techniques such as lazy loading, deferred loading of non-critical content, ensuring faster initial page rendering.
Implementing HTTP/2 and HTTPS: Upgrade to the HTTP/2 protocol to enable multiplexing and concurrent loading of multiple resources, enhancing overall page loading speed. Additionally, ensure your website is served over HTTPS, ensuring encrypted data transmission, thereby boosting security and gaining favor with search engines for better rankings.
Load Balancing and Redundancy: Implement load balancing mechanisms across multiple servers to evenly distribute traffic, avoiding overloads and ensuring consistent performance. Deploy redundancy strategies to enable failover in case of server failures, minimizing downtime and ensuring uninterrupted access to content.
Mobile Optimization: Prioritize mobile optimization by embracing responsive design principles and delivering optimized content specifically tailored for mobile devices. Leverage CDN capabilities to deliver fast and customized content to mobile users, enhancing their browsing experience.
Monitoring and Performance Analysis: Regularly monitor website performance using analytics tools and CDN-specific metrics. Analyze load times, user behavior, and potential bottlenecks to identify areas for continuous improvement. Utilize performance analysis to make data-driven optimizations and refine website speed.
Geolocation and Edge Caching: Leverage the CDN’s geolocation capabilities to deliver targeted and customized content based on user location. Employ edge caching strategies to pre-cache content closer to end-users, minimizing latency and ensuring faster access to frequently accessed content.
Continuous Testing and Improvement: Conduct routine performance tests, A/B testing, and analyze user feedback to identify areas for continuous improvement. Implement iterative enhancements and optimizations to refine website speed and user experience continually.
Security Measures and DDoS Protection: Leverage CDN security features to fortify your website against threats like DDoS attacks, malicious bots, and unauthorized requests. Ensure robust security measures are in place without compromising website speed, ensuring a secure and seamless user experience.
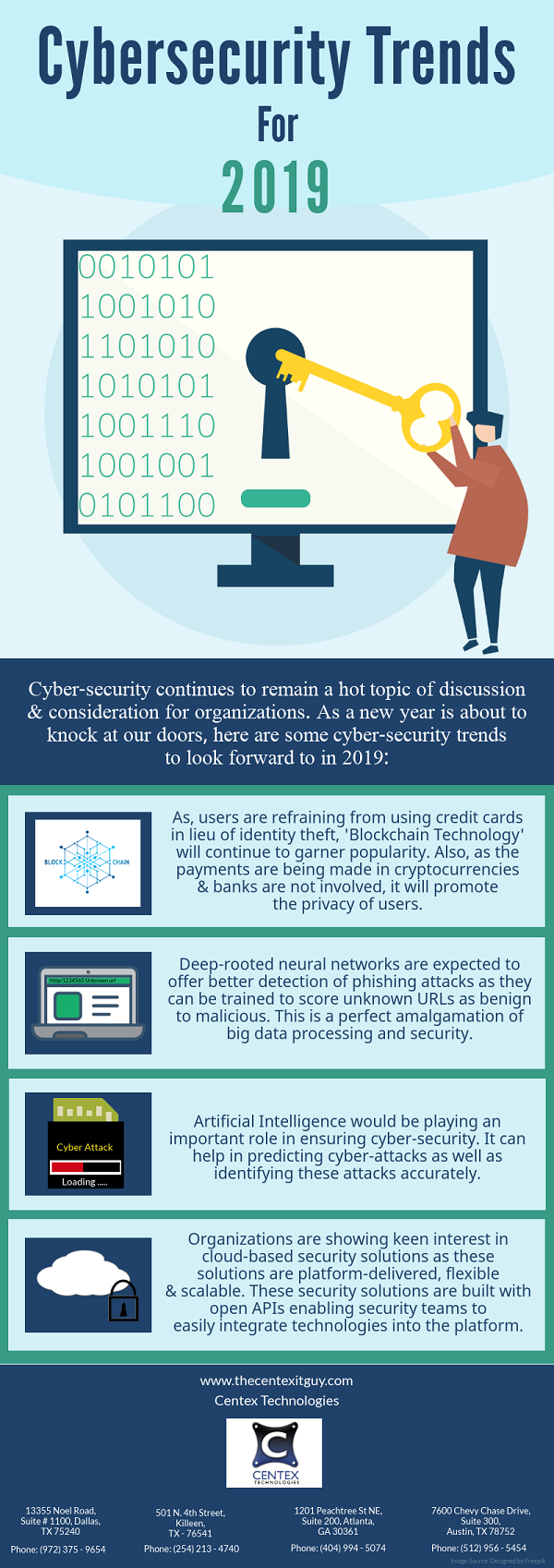
For more information on IT network solutions, contact Centex Technologies at Killeen (254) 213 – 4740, Dallas (972) 375 – 9654, Atlanta (404) 994 – 5074, and Austin (512) 956 – 5454