Undoubtedly using location-based services like Google maps, taxi services, etc. has made our life easier, however, location tracking or geo-tracking poses some real privacy threats as well. In order to understand these threats, it is first important to understand how this data is collected.
How Is Your Location Tracked?
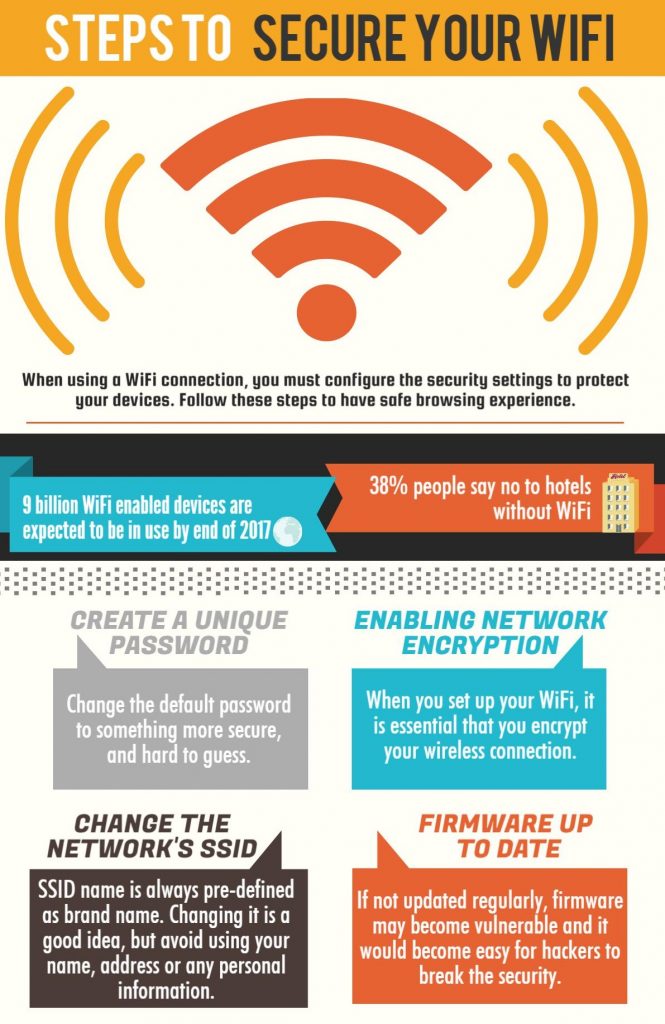
Location is tracked via your devices such as a laptop, mobile phones, tablets, smart-watches, smart jewelry, etc. In the case of a computer, your IP address can be used to track your location. If you are using a mobile device, the location is tracked via GPS, cellular tower data, Wi-Fi signals, and Bluetooth beacons.
A number of popular apps also track your location such as Google Maps, Facebook, Yelp, Uber, dating apps, etc. Some apps may track your location even after you have turned off location tracking in your mobile settings. A common example is Facebook. The app can track your location by your city mentioned in the profile or check-ins.
Additionally, information about your location is also revealed by the metadata attached to your photos. Most mobile phones and digital cameras embed information such as GPS coordinates or Geotags when you take a photo. When such photos are posted on a social media profile, the embedded information is also shared along.
What Kind Of Information Is Revealed By Location Tracking?
Location tracking can be used to disclose a variety of information:
- Where do you live
- Your financial status based on where you live
- Your place of work
- The regular route of travel
- Frequently visited stores
- Your real-time location
- If you are on a vacation and where are you staying
These are some common types of information that can be disclosed by location tracking.
Privacy Concerns Caused By Disclosure Of Such Information:
- Stalking & Harassment: Availability of detailed information about your location increases your risk of being stalked or harassed. If a stalker knows your frequently visited places, he can easily identify a place and the best time to confront you.
- Robbery: Burglars can get hold of sufficient information about you by eyeing your location tracks. This enables them to know when you won’t be home or if you follow a secluded path to your work. Discloser of such private information puts you in a danger.
- Contextual Advertizing: Contextual advertizing is a rising problem among social media users. Marketing professionals pay a high price for access to personal information such as location data of individuals. This helps them in understanding the user behavior to modify their advertizing campaign accordingly. This has led to a rise in the number of cyber-criminals trying to track the location of individuals for building databases that can be sold to organizations.
- Frauds: Fraudsters can gain access to your location data for building and studying your individual profile. This profile helps them to have a sneak-peak in your personal life to fabricate a fraud.
For more information on privacy concerns arising out of location tracking, call Centex Technologies at (254) 213 – 4740.