Most consumers believe that cyber risks only affect laptops or desktop computers. Mobile phones, in fact, have become the new focus of cyber assaults. The ever-increasing number of mobile phone users is a primary driver of this transition. Additionally, the enhanced capability of mobile phones has contributed to this transition.
The majority of mobile phone users nowadays use these devices to conduct most operations, such as making online payments, checking emails, storing personal data, connecting to their organizational network, and so on. As a result, mobile devices serve as a pool of opportunities for cybercriminals.
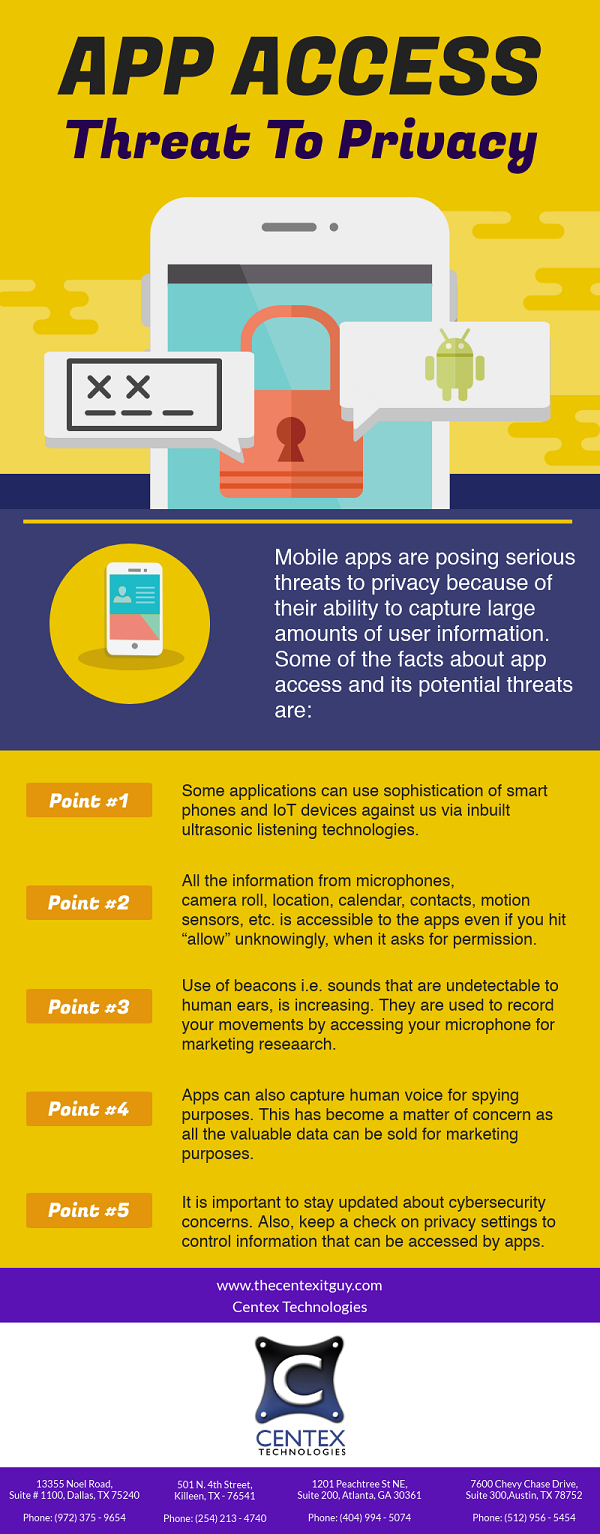
Another key factor that makes mobile phone users extremely vulnerable is a lack of knowledge about potential cyber security threats. The first step in addressing these threats is to get completely educated on the potential hazards.
Here is a list of some of the mobile security threats:
- Malicious Apps: Hackers frequently employ fake mobile apps with concealed malware and viruses. These programs are made to look like legitimate applications like games, instant messaging apps, or even antivirus software. The interface, including the layout, theme colors, fonts, and so on, is made to look like authentic apps in order to deceive mobile phone users into downloading false hacked apps. These apps, once downloaded and installed on a mobile device, can perform a variety of actions such as reconfiguring device settings, installing mobile ransomware, sending unauthorized communications, making social media posts, hacking user accounts, copying and sending personal photos to a third-party server, and so on.
- Mobile Greyware: This type of cyber-attack is less severe than a mobile virus, but it is more widespread. Mobile greyware refers to apps that do not include identifiable malware but can nevertheless harm the mobile device. These programs may be configured to control actions such as tracking the user’s location, monitoring web browsing history, boosting cell costs through unlawful internet access, and so on. ‘Madware’ or ‘Mobile Adware’ is a common type of mobile greyware. It may include apps that display unwelcome adverts in the notification area, substitute the call tone with a speech commercial, or disclose mobile data such as the contact list.
- Smishing: Smishing is a common term used for SMS phishing. It is a type of tactic used by hackers to target users via text messages. It is a preferred practice as it allows geographic targeting of victims. The fraudsters may pose as a local bank or credit union and send messages to locally present mobile users. The messages may include compromised links for stealing user information.
- Fake Networks: Similar to laptops or desktops, it is never a good idea to access an open Wi-Fi over a mobile device. Hackers can exploit these networks to intercept information such as emails, messages, login credentials, etc.
Centex Technologies provide complete IT security solutions for businesses. For more information, call Centex Technologies at (254) 213 – 4740.