PDF Version: Security-Vulnerabilities-in-IoT-Devices
Tag: IoT Security
Cyber security strategies aim at protecting any user or organization’s inter-connected systems, hardware, software, and data from cyber attacks. Absence of stringent cyber security strategies can offer an opportunity for hackers to access the computer system and network and misuse organization’s data such as trade secrets, customer data, etc.
In order to formulate an efficient cyber security strategy, it is imperative to pay heed to all areas of cyber security.
Following are different areas of cyber security:
- Critical Infrastructure Security: This area of critical infrastructure security consists of cyber-physical systems that modern societies rely on. Some examples of such systems include electricity grid, water purification, traffic lights, shopping centers, hospitals, etc. Hackers can attack the vulnerable infrastructure systems to gain access to connected devices. Organizations which are responsible for managing the infrastructure systems should perform due diligence to understand the vulnerabilities for society’s safety. Other organizations which are not responsible for the systems but rely on them for some part of their business operations should develop contingency plans to be prepared for any cyber attack or network breach that can be launched via an infrastructure system.
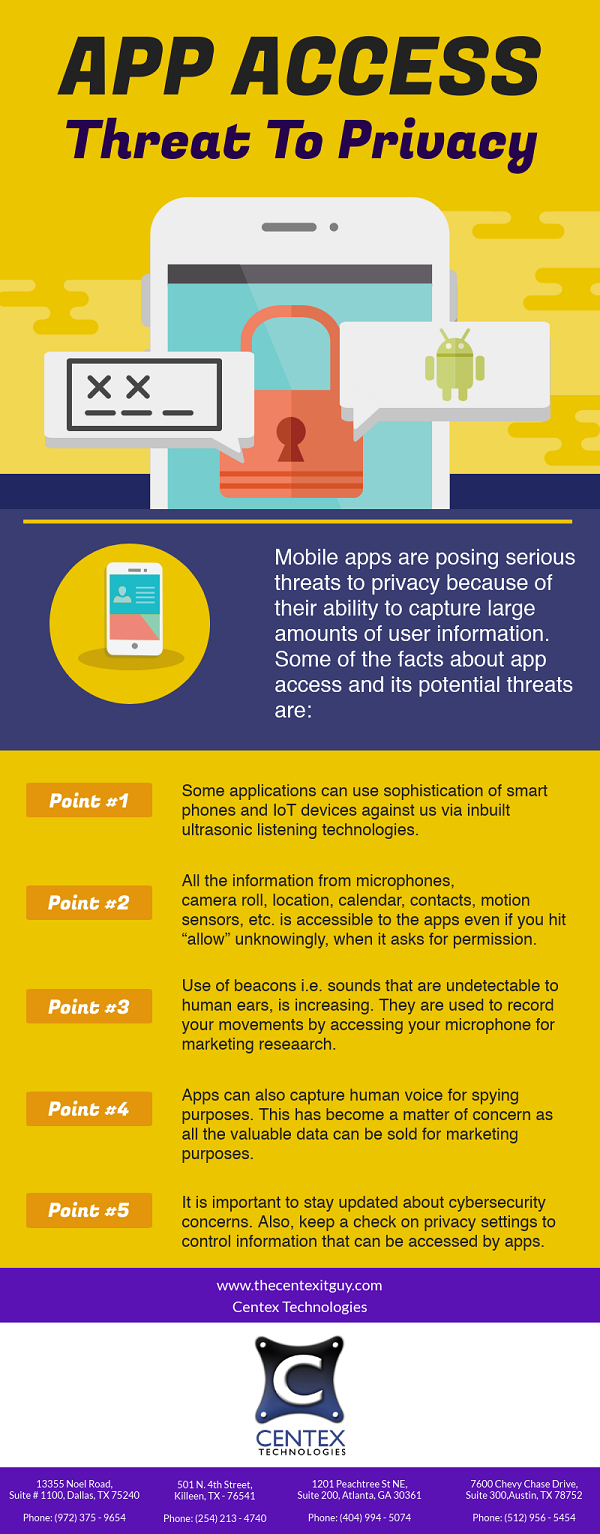
- Application Security: It is one of the most important areas of cyber security strategies of an organization. The branch of application security uses both software and hardware methods to tackle external threats that can arise in development or implementation stage of an application. As applications are majorly accessible over network, they are highly vulnerable. Thus, it becomes highly important to include application security in cyber security strategy of an organization. Types of application security include antivirus programs, firewalls, and encryption programs. Application security techniques ensure that unauthorized access to applications is prevented. Also, these techniques can help organizations in detecting sensitive data sets and implementing relevant measures to protect these data sets.
- Network Security: This area of cyber security guards an organization against unauthorized intrusion of internal networks due to malicious intent. Network security protocols inhibit access to internal networks by protecting the infrastructure. For better management of network security monitoring, network security teams use machine learning to flag abnormal traffic and issue threat alerts in real time. Common examples of network security protocols include multi-level logins, password security, etc.
- Cloud Security: Cloud security is a software-based security tool that monitors and protects organizational or personal data stored in cloud resources. Increasing use of cloud services has made way for stringent cloud security strategies.
- IoT Security: IoT devices can be highly vulnerable and open to cyber security attacks for numerous reasons including unawareness of users. Threat actors target IoT’s data centers, analytics, consumer devices, networks, legacy embedded systems and connectors. So, organizations have to implement stringent IoT security protocols.
For more information on different areas of cyber security, contact Centex Technologies at (254) 213 – 4740.