There has been an exponential increase in cyber-attack instances across the globe. This has led to a need for more advanced data protection and cyber security solutions which can defend organization’s IT systems and can protect business and consumer’s data. In such a scenario, newer technologies play a very important role in providing state-of-the-art data security solutions.
Some of the prominent technologies that are giving rise to possibilities of better data security in future are:
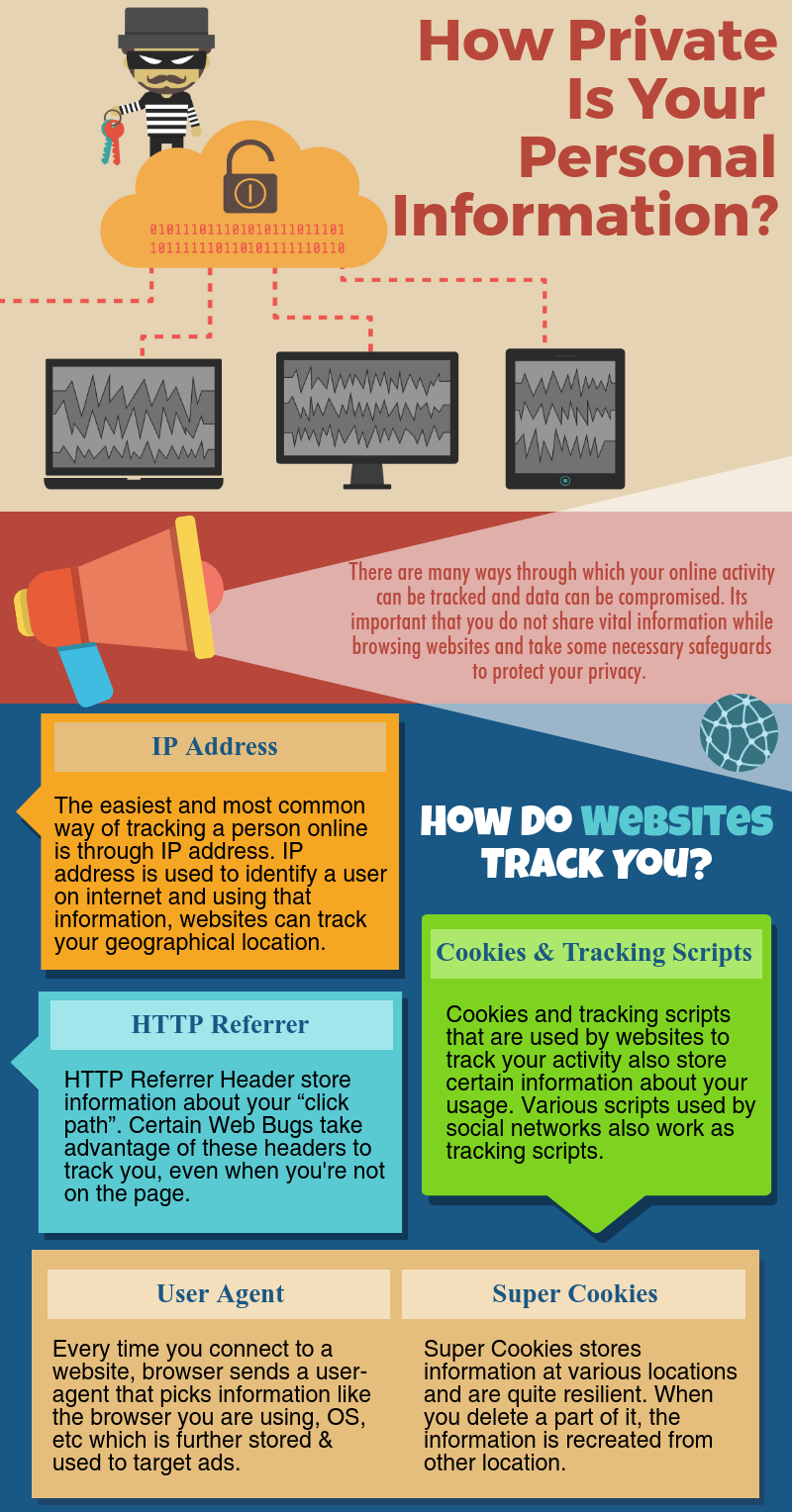
- Hardware Authentication: It is easier for hackers to get access to information systems due to inadequate passwords and usernames. This compromises sensitive data and urges the experts to come up with strict authentication methods. One of the ways, to accomplish this, is the development of user hardware authentication. Hardware authentication can be particularly essential for Internet of Things where it is important to ensure that any device seeking connectivity has the authorization to do so.
- User Behavior Analytics (UBA): It is a cybersecurity process that detects threats, targeted attacks and financial frauds. It gains information about network events like any kind of malicious behavior by attackers, unauthenticated usernames and passwords, etc. UBA is a valuable tool to train employees for adopting better security practices.
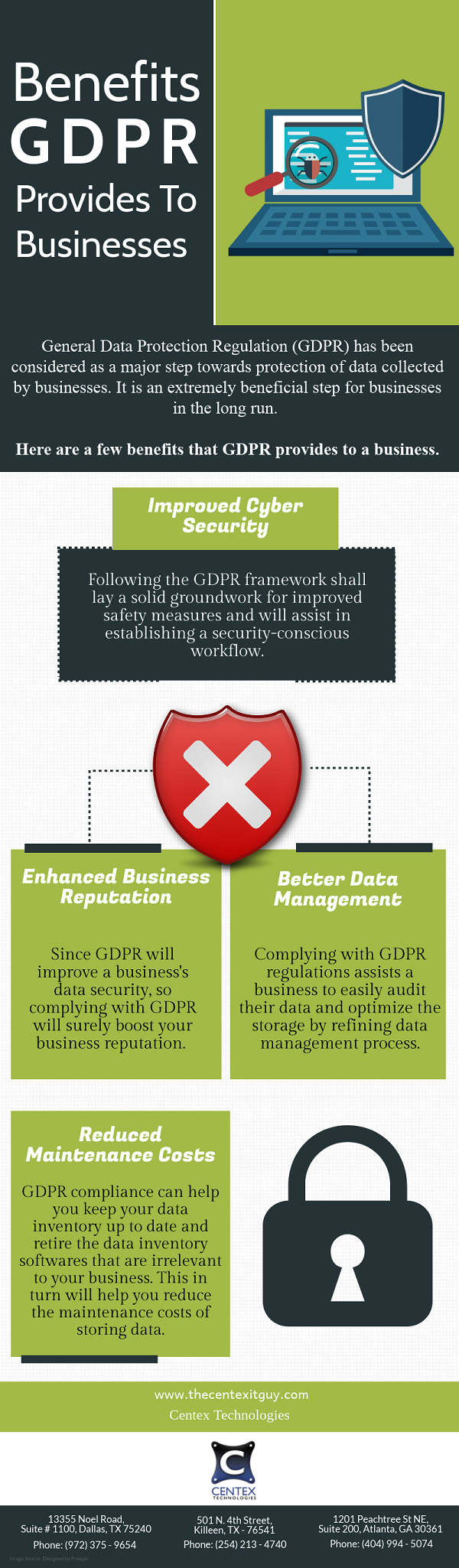
- Data Loss Prevention: Encryption of data can protect it on field and sub-field levels. Though any business process can be performed on encrypted data in its protected form, the attackers cannot monetize data even if they conduct a successful breach. For data loss prevention to work well, enterprises should ensure compliance to data privacy and security regulations.
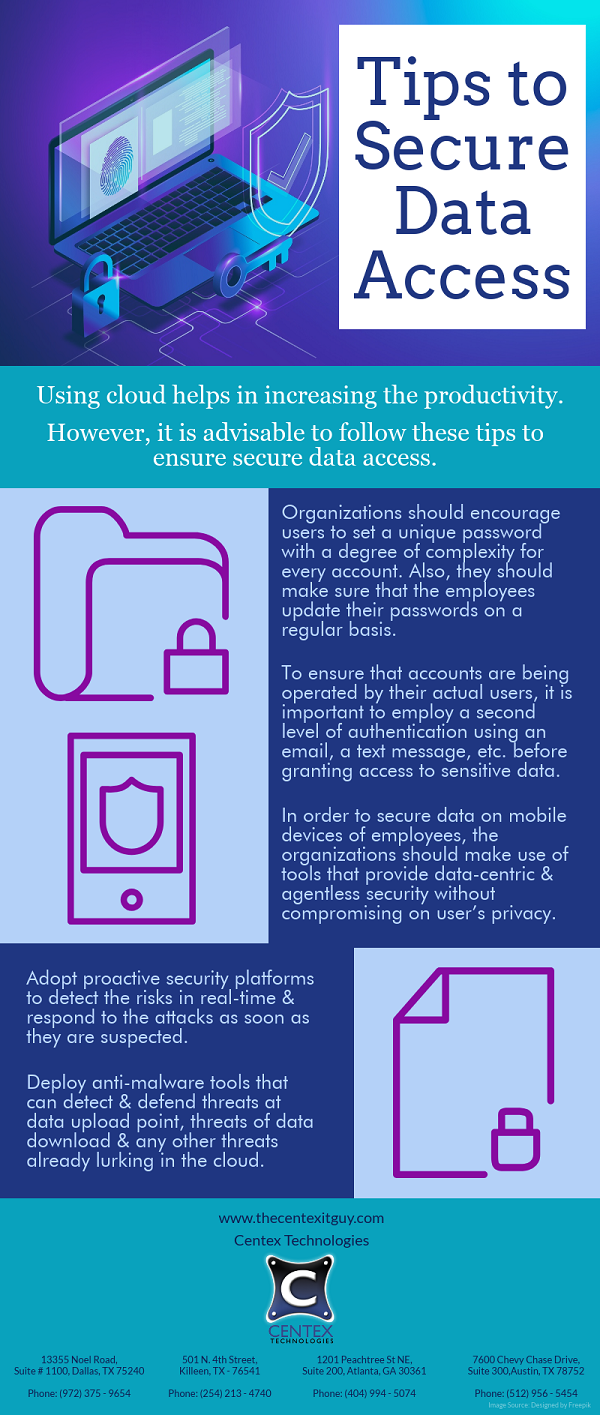
- Cloud Technology: Transformation of system security technology will be impacted significantly through the cloud. Users have embraced cloud technology to store vast amount of information that is generated on daily basis. Migration from on-premise data storage and development of information systems security to be used in the cloud is emerging gradually.
- Deep Learning: Technologies like deep learning consist of artificial intelligence and machine learning. Experts have a significant deal of interest in these technologies for the purpose of system security. They focus on anomalous behavior as whenever AI and machine learning are fed with right data regarding a potential security threat, decisions are made to prevent attacks depending upon immediate environment without human input. Deep learning techniques have made it possible to analyze different entities that are found in an enterprise both at micro and macro level.
Combination of these new technologies and fundamental security controls can help in ensuring that the confidential information of an organization is safe. For more information on emerging data security technologies, call Centex Technologies at (254) 213-4740.