What Is A Network Security Attack?
A network security attack is an action or attempt aimed at gaining unauthorized access to an organization’s network. The objective of these attacks is to steal data or perform other malicious activity. Network attacks can be classified into two main types:
- Passive Attack: In this type of attacks, attackers gain access to the organization’s network and monitor or steal data but without making any change to the data.
- Active Attack: In an active attack, attackers not only gain unauthorized access to the data but also modify data by deleting, encrypting, or otherwise harming it.
The main focus of network security attackers is to bypass peripheral security of an organization and gain access to internal systems. But in some cases, attackers may combine other types of attacks such as endpoint compromise, malware induction, etc.
What Are Common Network Security Threats?
The types of network security threats are defined by the threat vectors used by the network security attackers to penetrate the network:
- Unauthorized Access: The attackers gain access to the network without receiving legitimate permission. Some causes of unauthorized access are weak passwords, insufficient protection against social engineering, compromised accounts, and insider threats.
- Distributed Denial of Service Attacks: Attacks build a network of bots and compromised devices to direct false traffic at the organization’s network or server. This overwhelms the server resulting in interruption of security layers.
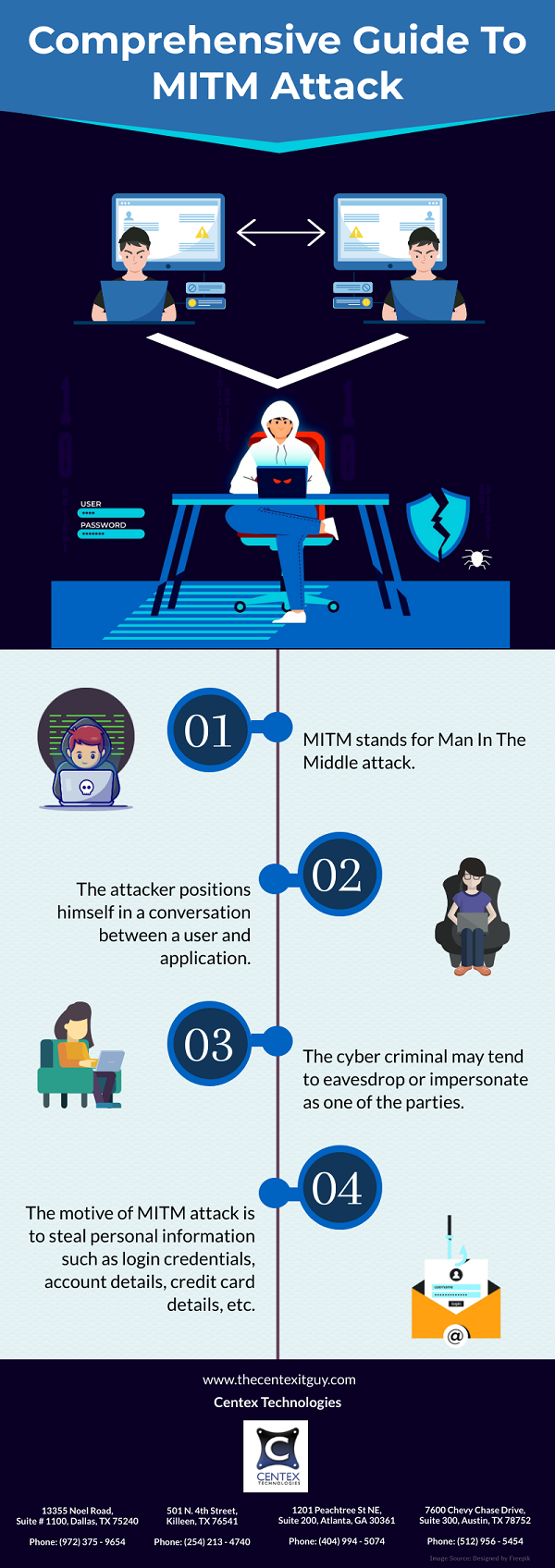
- Man In The Middle Attack: It involves interception of traffic between organization’s network and external sites. If the communication is insecure, attackers can circumvent the security and steal the data being transmitted.
- Code & SQL Injection Attacks: Many websites accept user inputs through forms but do not sanitize them. Attackers fill out these forms or make an API call, passing malicious code instead of expected data values. Once the code is executed, it allows attackers to compromise the network.
What Are The Best Practices To Stay Protected Against Network Security Threats?
Following are some best practices to stay protected against network security threats:
- Segregate the organization’s network
- Regulate internet access via proxy server
- Place security devices correctly
- Use network address translation
- Monitor network traffic
- Use deception technology
For more information on things to know about network security threats, contact Centex Technologies at (254) 213 – 4740.