28th August, 2017
Threat Monitoring is a technique used to improve security of a system or a facility and helps in identifying a potential security breach in the network. It aims at continuously monitoring a network to check if there are any security violations on the device. For example, whenever a person makes repeated failed login attempts, a warning signal is sent to the monitoring center that an intruder might be trying to guess the password.
How It Works?
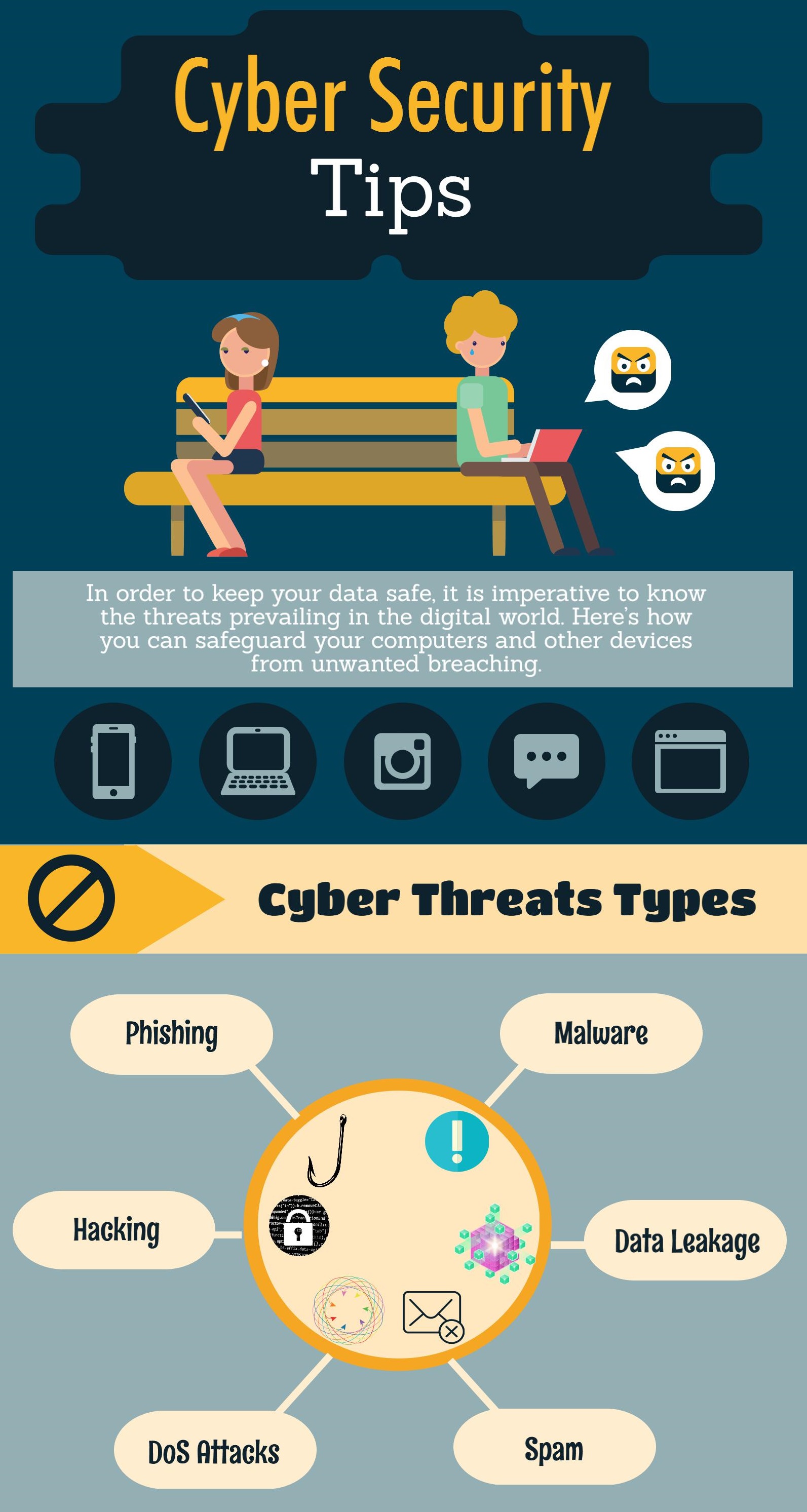
Threat Monitoring involves day-to-day analysis and evaluation of security data to identify any cyber-attacks or breaches. It collects and correlates information from various processes to identify patterns in order to check if there are any threats to the system.
Benefits
Threat Monitoring helps to detect activities such as an outsider breaching into the network or if any internal process is compromised. While it can be difficult to detect such susceptibilities in overall system security, Threat Monitoring provides a proactive solution to identify such issues beforehand. The technique works by recognizing the anomalies of such illegal activities by correlating information about networks with factors like IP address and URLs.
Threat monitoring provides several benefits such as:
- It can help security professionals to check what is happening on their network.
- It also assists them to find any vulnerability in their network or applications and how to fix these problems.
- Threat Monitoring helps to check if the network usage aligns with company’s policy agreement.
Need For Threat Monitoring for Businesses
Here are the two major reasons why threat monitoring is necessary for small businesses:
- The data of your organization is more important than you think. The biggest mistake that few companies make is that they think they have nothing worth stealing. From a small password to the employees’ data, there is a lot of information that a company wants to keep private. Threat monitoring can help to prevent such issues.
- You are considered an easy target. You are at a same level of risk as large companies, even though you have less budget to deal with, because these criminals take the path of least resistance.
Threat Monitoring can prove to be a reliable tool when it comes to the security of your network and online portal, no matter how big or small is your work. Proactive approach of Threat Monitoring makes it important for businesses to implement it across their network.
To know more about threat monitoring and its benefits, contact Centex Technologies at (855) 375 – 9654.