Tag: Botnets
May 7, 2016
Botnets are a group of malware infected computers that are controlled by cybercriminals. They use a specially designed malware program, known as bot, to breach the security of the targeted computers and gain access to its administrative accounts so that they can be managed from a remote server. The network of compromised computers is then used to send out spam emails, initiate denial of service and phishing attacks as well as commit financial frauds. The bots usually remain undetected and operate in background programs, making it difficult for the users to remove the malicious program from their computer system.
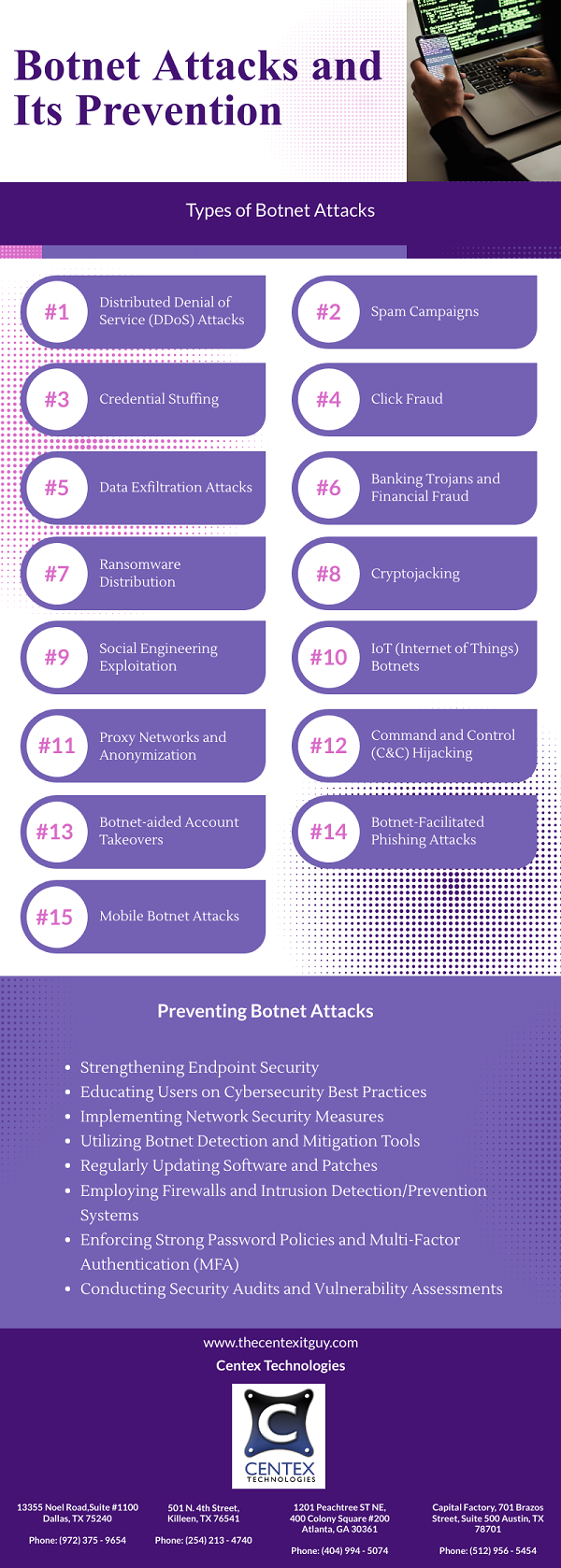
Below are some tips to protect against botnets:
- Be Careful With Pop-Ups And Suspicious Links: Make sure you do not click on pop-ups that appear randomly on a website. Most of the ads that show a warning message or prompt you to download an anti-virus software are laden with malware which can compromise the security of your computer. Also, avoid visiting websites that appear to be fake as they can download malware the moment you open them.
- Do Not Open Email Attachments: You should not click on or download email attachments from unknown senders. Most of these contain malware disguised as an important document, such as a tax form or sales invoice. As soon as the user attempts to open the file, the malware gets activated.
- Switch Browsers: Another effective technique for protecting against botnets is to use a browser other than the popular ones. Most malware are designed according to the security configurations of the browsers used by most people. Switching your web browser can lower the risk of botnet attack to a great extent.
- Improve System Security: Install anti-virus, spyware and anti-malware software on your computer to scan as well as remove any potentially malicious programs. Make sure you subscribe to automatic updates or install the newer versions to avoid making your system an easy target for the hackers. USB flash drives and other removable storage devices should be used cautiously as they can easily transmit malware. Also, disable the auto run feature on your computer to avoid installing software and programs from unknown sources.
- Use Secure Credentials: Use a difficult username as well as strong password and keep them in an encrypted format. For better security, you can adopt 2 factor authentication so that even if the hacker is able to breach your password, he will not be able to gain access to the account.
We, at Centex Technologies, can help to improve the cyber security at your business firm in Central Texas. For more information, feel free to call us at (855) 375 – 9654.