Tag: Botnet Attacks
The word ‘Botnet’ is derived from combination of two words – ‘Robot’ & ‘Network’. It can be defined as a number of computers that have been infected by malware such that they can be remotely controlled by the hackers to form a network which is then used to launch attacks on other users. The hackers exploit the resources of infected machines to launch different attacks such as DDoS, data breaches, etc.
How do Botnet Attacks Work?
A botnet attack is launched in three steps:
- Finding vulnerable devices
- Spreading malware in these devices
- Gaining control over devices
Cybercriminals or hackers use three different ways to infect and gain control of devices to form their Botnet or ‘Zombie Army’.
- Installation of a malicious software
- Launching a direct hacking attack
- Using an automated program to monitor the internet & locate vulnerable devices
If an infected device is connected to a system, hackers can spread the malware laterally and gain control of other devices linked to the same network. Once the devices have been infected, they are either controlled using either remote software or Control-And-Command software. These controlled devices are then used to act according to the hacker. Some common actions performed using botnets include sending spam emails, launching multiple server requests, creating internet traffic towards a website, and increasing the number of downloads for a software or application.
In order to prevent a botnet attack, it is first important to understand different types of botnet attacks.
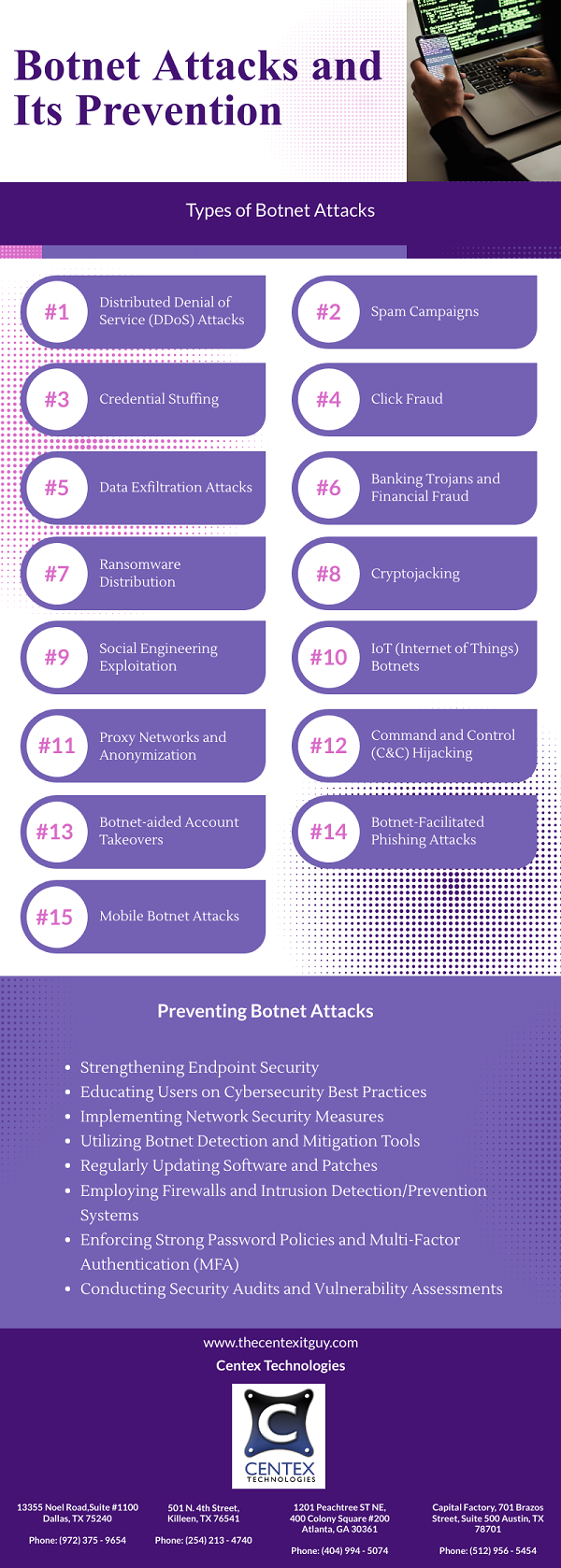
Types of Attacks Performed Using a Botnet:
As a large number of devices are a part of a botnet, the hackers have access to a large bank of resources such as computation capacity, storage, etc. It equips the hackers to launch different types of attacks such as:
- Phishing Attack
- Distributed Denial-of-Service Attacks
- Bruce Force Attacks
- Cryptocurrency Mining
- Browser Add-on Installation
- Personal Information Theft
- Device Bricking
Tips to Prevent Botnet Attacks:
Before understanding ways to prevent a botnet attack, let us first look at why it is challenging to prevent or protect yourself against a botnet attack.
- As a large number of devices are connected to a botnet, it makes it difficult for cyber security tools to screen out potentially lethal access requests sent to a website or API.
- IoT devices with IP addresses are more vulnerable than computers and can be easily manipulated by hackers to become a part of botnet. These devices are used to launch slow attacks and are more difficult to detect.
- Botnets are continuously modified to exploit new vulnerabilities making it difficult to understand the behavioral pattern.
Here are some tips to prevent botnet attacks:
- Up-To-Date Devices: Botnets are designed and modified to exploit existing vulnerabilities in software or app. So, make sure that every device connected to your network installs a software update or security patch. Software updates are launched to fix vulnerabilities in previous versions. This helps in preventing a botnet attack by closing the backdoor or software vulnerability.
- Network Monitoring: Use advanced analytics to regularly monitor incoming and outgoing traffic & compare it with normal network behavior. This helps in detecting unusual activity or anomalous behavior which can be a sign of a botnet attack. Early detection helps in implementing effective measures to combat the attack.
- Monitor Access or Login Attempts: Botnets are commonly used to launch ‘Bruce Force Attacks’ by testing multiple usernames and password combinations to gain unauthorized control of user accounts. Monitor the failed login attempts to detect & prevent a botnet attack at the nascent stage.
- Manage Admin Access: Exercise thorough consideration when granting admin access. Understand the role of an employee and analyze if he needs admin access to perform his duties. Limiting admin access helps in reducing the risk of both internal as well as external attacks.
- Cybersecurity Hygiene: Establish strong cybersecurity hygiene across your organization. This can be achieved by educating employees about cybersecurity best practices such as the use of strong password, multifactor authentication, avoiding link clicks or downloads from unknown sources, etc.
- Be Cautious: Look out for early signs of a botnet attack. Some of these signs include slow speed of device, change in homepage of browser, random pop-ups, etc. If any of these signs are spotted, run a thorough scan of the system and install a good antivirus software to remove any malicious software already installed or running on your device.
To know more about botnet attacks and ways to prevent a botnet attack, contact Centex Technologies at Killeen (254) 213 – 4740, Dallas (972) 375 – 9654, Atlanta (404) 994 – 5074, and Austin (512) 956 – 5454.
Enemybot is a new botnet that is conducting DDoS (Distributed Denial of Service) assaults on several routers and websites. It is attacking various routers and websites by leveraging existing vulnerabilities in ARM, BSD, x64, x86, and other architectures. Enemybot was identified by FortiGuard labs in mid-March.
This botnet is mostly based on the source code of Gafgyt, however it has been reported to borrow various modules from Mirai’s original source code. To avoid detection, the Enemybot employs a number of obfuscation techniques and hides Command and control (C2) server on the TOR network. The Enemybot botnet spreads and assaults other IoT devices through a variety of tactics. It attempts to gain access to systems using weak or default credentials by logging into devices with a list of hardcoded username/password combinations. By running shell commands, the bot also attempts to infect misconfigured Android devices that expose the Android Debug Bridge port (5555). Enemybot has been observed infecting Seowon Intech and D-Link routers as well as abusing a previously disclosed iRZ router vulnerability.
The bot leverages a number of known and previously disclosed loopholes, which include: –
- SEOWON INTECH SLC-130 and SLR-120S routers are vulnerable to CVE-2020-17456.
- Earlier D-Link routers were vulnerable to CVE-2018-10823.
- CVE-2022-27226 affects iRZ mobile routers.
- CVE-2022-25075 to 25084 affects TOTOLINK routers, which were formerly used by the Beastmode botnet.
- CVE-2021-41773/CVE-2021-42013 is a vulnerability that affects Apache HTTP servers.
- CVE-2018-20062: This vulnerability affects the ThinkPHP CMS.
- CVE-2017-18368 is a vulnerability that affects Zyxel P660HN routers.
- CVE-2016-6277 is a vulnerability that affects NETGEAR routers.
- CVE-2015-2051 is a vulnerability that affects D-Link routers.
- CVE-2014-9118 is a vulnerability that affects Zhone routers.
Once one of the foregoing problems has been exploited, the bot will use the shell command LDSERVER to download a shell script from a URL that the C2 server will dynamically update. The script then downloads the real Enemybot binary, which is adapted to the target device’s architecture. If the download server goes down, the botnet managers can update the bot clients with a new URL. The bot connects to its C2 server after being placed on a device and waits for new orders.
Enemybot’s Capabilities
Enemybot connects to the C2 server and waits for orders to be executed when a device is infected. Although the majority of the instructions are connected to DDoS assaults, the virus is not just focused on them. Fortinet presents the following set of supported commands: –
- ADNS: Perform a DNS amplification attack with ADNS.
- ARK: Stealth survival while launching an attack on the game’s servers.
- BLACKNURSE — Flood the target with ICMP packets indicating that the destination port is unreachable.
- DNS – Inundate DNS servers with DNS UDP requests that have been hardcoded.
- HOLD – Flood the target with TCP connections and keep them alive for a certain amount of time.
- HTTP — Send a flood of HTTP requests to the destination.
- JUNK — Flood the destination with non-zero-byte UDP packets at random intervals.
- OVH – Send custom UDP packets to OVH servers.
- STD — Send a flood of random-byte UDP packets to the destination.
- TCP — Send a flood of TCP packets to the target with forged source headers.
- TLS — Carry out an SSL/TLS attack.
- UDP — Send UDP packets with forged source headers to the destination.
- OVERTCP — Use randomized packet delivery intervals to launch a TCP assault.
- STOP — Put an end to continuous DoS assaults.
- LDSERVER – Update the exploit payload download server.
- SCANNER — SSH/Telnet brute-force attacks and vulnerabilities spread to additional devices.
- TCPOFF/TCPON — Turn the sniffer off or on at ports 80, 21, 25, 666, 1337, and 8080, potentially to gather credentials.
Preventing Botnet Attacks
Always apply the latest available software and firmware updates for your product to prevent Enemybot or any other botnet from infecting your devices and recruiting them to malicious DDoS botnets.
One of the most common signs that your router may be infected with a botnet malware infection is that the router may become non-responsive, internet speeds drop, and the router becomes hotter than usual. In such a scenario, you should restart the router and change the passwords. It is also advised to take services of specialized cyber-security professionals to find and weed out the problem.
Centex Technologies provide state-of-the-art cybersecurity and network security solutions for businesses. To know more, contact Centex Technologies at Killeen (254) 213-4740, Dallas (972) 375-9654, Atlanta (404) 994-5074, and Austin (512) 956-5454.